How to Install Kali Linux as an App in Windows 10
By Jack Giardina on March 23, 2018
Introduction
Recently Kali Linux was released as an application in the Microsoft Store. Through utilization of the Windows Subsystem for Linux (WSL) compatibility layer, its now possible to install Kali in a Windows environment. WSL is a feature in Windows 10 that enables users to run native Linux command-lines tools, Bash, and other tools previously not available. The feature was designed primarily for developers, gives Windows 10 added versatility, and presents an alternative option to virtualization. Below is a detailed guide on how to get WSL Kali up and running.
Installing Kali Linux in Windows 10
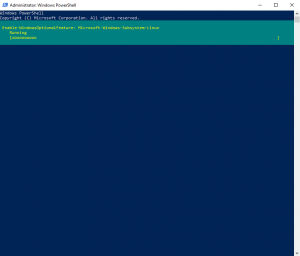
1. Run powershell as an administrator and execute the following command:
Enable-WindowsOptionalFeature -Online -FeatureName Microsoft-Windows-Subsystem-Linux
Reboot when prompted
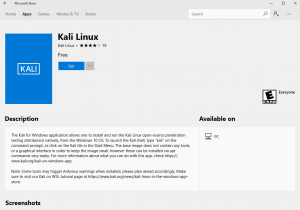
2. Download the Kali Linux app (134MB) from the Microsoft Store and launch once it completes.
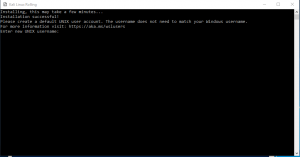
3. Create a user account during the installation process (copy new credentials down!).
4. Run the command cat /etc/issue to verify the environment.
5. Locate the newly created Kali directory in Windows. This directory can typically be found at C:Users<youraccount>AppDataLocalPackagesKaliLinux.XXX. In order to view this directory it will be necessary to reveal hidden items (view -> show hidden files).
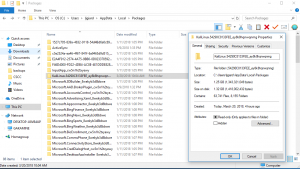
6. Copy the file path to the Kali directory (C:Users<youraccount>AppDataLocalPackagesKaliLinux.XXX) and then add it as a security exception in Windows Defender (Windows Defender Security Center -> Virus and Threat Protection -> V&T Protection Settings -> A/R Exclusions -> Add Exclusion -> Folder).

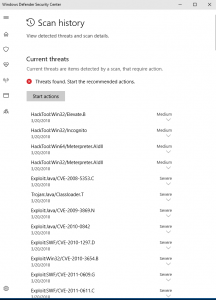
It is important to point out that if this step is not accomplished before installing certain packages, Windows Defender is going to throw a fit and identify all the associated files as malicious. The most likely result is that Windows Defender will become overwhelmed and either begin crashing or working intermittently. Shown below is a brief snapshot of the alerts that can be generated by the metasploit-framework if the exception is not added first.
7. Run the command sudo apt-get update (ignore the error – W: http: aptMethod::Configuration: could not load seccomp policy: Invalid argument).
8. Run the command sudo apt-get dist-upgrade.
9. Begin installing packages as desired. For the sake of this demonstration nmap, wireshark, hashcat, and the metasploit-framework were installed.
10. Run the command sudo apt-get clean.
11. Install and run xfce4 and XRDP. Xfce4 is a free and open-source desktop environment for Unix operating systems. In this instance it will provide a visual environment for any packages you install that require the use of a GUI. XRDP is a free and open-source remote desktop protocol server that can be utilized to connect to the newly created desktop environment.
Run the following commands:
wget https://kali.sh/xfce4.sh
cat xfce4.sh (verification)
sudo sh xfce4.sh (runs installation script) *this may take a while depending on the internet connection
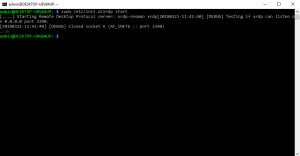
12. Start the remote desktop server on port 3390 by running the following command: sudo /etc/init.d/xrdp start.
13. Open a remote connection to the server (start -> run -> mstsc) @ localhost/127.0.0.1:3390.
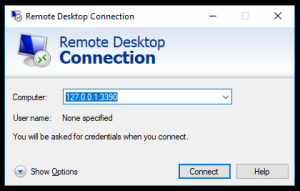
17. Enter the credentials for the kali user created earlier. In order to connect to the remote environment it may also be necessary to add an exception in Windows Firewall for Remote Desktop (Control Panel -> Windows Defender Firewall -> Allow and app or feature through firewall -> Remote Desktop).

18. After experiencing inception, logout of the remote session (click the logo in the top right and uncheck save session on the way out).

19. Shutdown the xrdp server by running the command: sudo /etc/init.d/xrdp stop.
20. Logout of the kali instance (exit).
Final Thoughts
Installing Kali Linux as an app in Windows allows for the utilization of many useful tools that were not available previously. By running Kali through WSL as opposed to inside a virtual environment its also possible to experience performance gains in processor reliant frameworks such as hashcat. Shown below are the performance results for hashcat running virtually vs. hashcat running in the WSL environment. The system specifications in this instance were as follows:
- Intel i-7 4870HQ Processor @ 2.5 GHz
- 16 GB DDR3 RAM @ 1600 MHz
- Radeon R9 M370X 2GB GDDR5 Video Card

In the WSL environment, hashcat was able to crack a list of 8 MD5 hashes in a little under two seconds vs. the 11 seconds it took when running in a virtual environment. This boost in performance here (500%+) is notable and could prove useful under certain circumstances. One of the drawbacks to running Kali via WSL vs. running it natively is that WSL does not support the use of raw sockets (A network socket that permits direct sending/receiving of IP packets without any protocol-specific transport layer formatting). The pros and cons of using Kali Linux in the WSL environment will become more clear over time, but for now it represents an interesting alternative to whats currently available.
SOURCES
Microsoft, https://docs.microsoft.com/en-us/windows/wsl/faq
Kali Linux, https://www.kali.org/news/kali-linux-in-the-windows-app-store/
-
Russia’s Cyber Strategies
Russia’s Cyber Strategies
12/2/2021 -
The Next Generation and Cyber Security
The Next Generation and Cyber Security
12/2/2021 -
Syniverse Short Message Service (SMS) Hack and Two Factor Authentication
Syniverse Short Message Service (SMS) Hack and Two Factor Authentication
12/2/2021